
Securing your entire organisation has never been easier. Duo’s two-factor authentication, remote access and access control products deploy fast in any environment. We help keep companies safer than ever before with minimal downtime and optimised productivity.
As a part of Cisco Secure’s comprehensive suite of security products, Duo helps your organisation — and every user in it — achieve security resilience. The product is easier to use, protects any device, integrates with any application — and it works!
Our customisable solutions offer dynamic cybersecurity that evolves with your organisation. Adapt to the changing threat landscapes faster with full-scale visibility and unmatched reliability, all from an interface so simple that anyone can use it.
Multi-Factor Authentication (MFA) is the practice of adding multiple unique authentication methods to user identity verification at login.
Two-Factor Authentication (2FA) – The practice of adding a second unique authentication method to user identity verification at login
Multi-factor authentication (MFA) is an access security product used to verify a user’s identity at login. It adds two or more identity-checking steps to user logins by use of secure authentication tools. Adding MFA keeps your data secure. With Cisco Secure Access by Duo, it’s easier than ever to integrate and use.

Identity Security – An essential security control in today’s digital world, identity security products are used to verify the user’s identity and prevent use of stolen passwords / compromised credentials
Secure Access – The idea that anyone who accesses data is properly verified to ensure all logins are benevolent and safe
Zero Trust – A cybersecurity strategy framework that encourages users and organisations to take added security measures, assuming that nothing can be trusted without proper verification. Zero trust is often described by the mantra of “never trust, always verify”
A malware attack which successfully siezes personal or company data, or locks users out and then demands monetary payment (ransom) in exchange for the stolen data. It is designed to deny or limit the user’s access to their system until the ransom is paid. Although, paying a ransom doesn’t guarantee data.

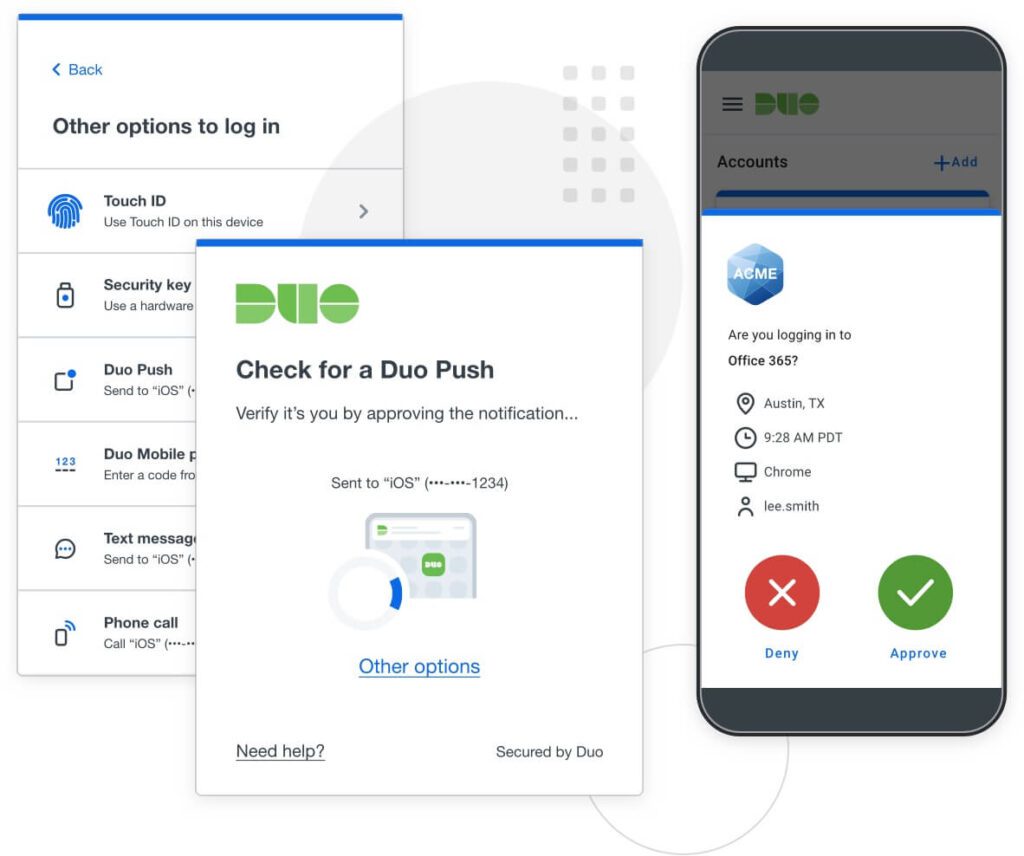
We’re the easiest MFA for users and administrators. Duo Push and Verified Duo Push are just two examples of the convenient, user-friendly MFA methods that we support. All a user has to do is download the Duo Push application onto their smartphone and voila: they’re ready to authenticate!
With Duo Password-less Authentication, users only have to verify once in a timeframe set by administrators, making it simpler than ever to log on securely.
Duo functions like a gateway for your existing and future IT infrastructure, and consequently it’s the perfect solution for growing businesses of any size. Set up new users and support new devices at any time, and protect new applications almost instantly — without impacting legacy technology.
Finally — a multi-factor authentication solution that isn’t a pain in the neck to roll out. Overall, Duo can be added to any existing environment or platform, and its self-enrollment feature makes it easy for users to get set up.