Hey there! Welcome to the world of WiFi security. It might seem like a really complex topic, but getting the right type of security for wifi in place is one of the most important things you can do to protect your data and your users. This guide is designed to cut through the jargon and give you the practical knowledge you need to make smart decisions.
Understanding Your WiFi Security Options
We're going to start from the ground up, explaining the real differences between encryption standards like WPA2 and WPA3 and why grabbing the latest one is a no-brainer. Think of this as your friendly roadmap, leading you from the basics of encryption all the way to more sophisticated authentication solutions.
Whether you're managing a busy network in Education, a bustling Retail space, or a corporate BYOD environment, we'll look at how solutions from industry leaders like Cisco and Meraki can help you build a secure and seamless wireless experience. Let's get your network locked down.
A Layered Approach to Protection
Securing a modern wireless network is about more than just picking a strong password. It's a layered strategy, combining solid, foundational encryption with smart user access controls. This way, you can be sure every connection is verified and shielded from potential threats.
The diagram below really brings this hierarchy to life. It shows how the primary encryption is the bedrock, with more advanced authentication methods built right on top of it.
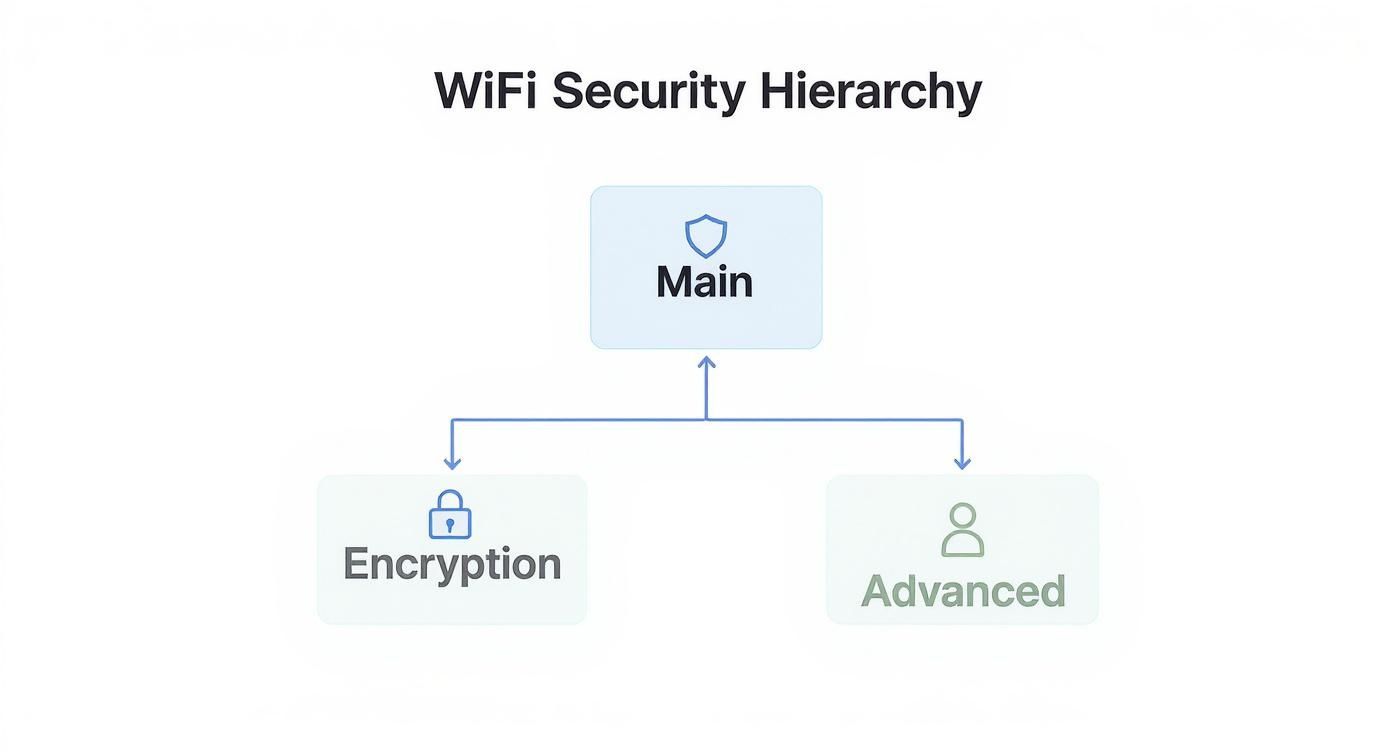
This visual makes it clear: truly effective security isn't an "either/or" choice. It's about combining the right tools to create a comprehensive defense.
WiFi Security Protocols at a Glance
To quickly see how the most common encryption methods stack up, take a look at this table. It's a handy cheat sheet for understanding where each protocol fits best.
| Protocol | Security Level | Common Use Case | Key Feature |
|---|---|---|---|
| WEP | Very Low | Legacy devices only (AVOID if possible) | Outdated and easily cracked |
| WPA | Low | Obsolete; replaced by WPA2 | Introduced TKIP, a temporary fix over WEP |
| WPA2 | Good | Home networks, small businesses | Uses strong AES encryption (the current standard) |
| WPA3 | Excellent | All new deployments, enterprise environments | Enhanced protection against password guessing |
This table highlights the evolution of WiFi security. While WPA2 is still widely used and generally secure, WPA3 is the clear winner for any new network setup, offering protections that are essential in today's environment.
Beyond the Basics for Guest WiFi
For so many organizations, especially in retail or corporate offices, guest wifi is a unique headache. You want to offer easy access, but you can't afford to put your internal network at risk. This is where the more advanced tools really shine.
Modern solutions go far beyond a simple shared password. They focus on identifying and managing every single user, turning your guest network from a potential liability into a secure, controlled asset.
Features like Captive Portals are a great example. They create branded login pages where users can connect through social login (social wifi) or simply agree to your terms of service. It’s a fantastic way to offer secure access on your Cisco and Meraki networks.
For even more control, technologies like IPSK (also known as EasyPSK) let you generate unique credentials for each user or device. This dramatically boosts security in BYOD environments and is a game-changer for sectors like education, where managing hundreds of individual student devices is just another Tuesday.
The Journey from WEP to WPA3 Encryption
To really get a handle on modern Wi-Fi security, it helps to look back at where it all began. The way we connect has changed dramatically, and so have the methods for protecting those wireless connections. You can see a clear line of progress, with each new standard fixing the holes left by the one before it.
It all started with WEP (Wired Equivalent Privacy). As the very first encryption protocol, WEP was a noble first attempt, but it didn't take long for security experts to find major flaws. Think of it like a cheap diary lock—it might stop a casual snooper, but anyone with a bit of determination could pop it open easily.
Today, WEP is completely obsolete. You should never, ever use it.
The Rise of WPA2
Realizing WEP was a sinking ship, the industry scrambled to create WPA (Wi-Fi Protected Access) as a stop-gap measure. But the real workhorse for more than a decade has been WPA2. This standard introduced AES (Advanced Encryption Standard) encryption, which is a much, much tougher security algorithm to crack.
For years, WPA2 was the gold standard, securing wireless networks in homes, coffee shops, and offices worldwide. It became the dominant type of security for wifi simply because it was a huge leap forward from the flimsy protection WEP offered.
But even a trusty standard like WPA2 eventually starts to show its age. New threats emerged that it wasn't built to defend against, especially on public and guest Wi-Fi networks.
WPA3: The New Standard for Security
That brings us to WPA3, the current champion of Wi-Fi encryption. WPA3 was built for the modern internet, specifically designed to shut down the vulnerabilities of its predecessors. Its key advantage is robust protection against offline brute-force attacks, which is when a hacker repeatedly tries to guess your password.
WPA3 makes this kind of attack almost impossible to pull off, even if a user has a relatively simple password. This is a game-changer for any public network, from a shop's guest wifi to a large corporate BYOD environment.
This protocol is a cornerstone of modern authentication solutions. Top-tier hardware from providers like Cisco and Meraki is built to support WPA3, empowering organizations in Education, Retail, and corporate settings to deploy the strongest encryption available.
If you want a deeper dive, our guide on what WPA3 is and why it matters has you covered. By moving to WPA3, you're not just meeting today's security standards—you're getting ready for the threats of tomorrow.
PSK vs. Enterprise: Which Wi-Fi Authentication Method is Right for You?
Strong encryption is your first line of defense, but it's only half the battle. The next critical question is: how do you control who gets onto your network in the first place? This is where authentication comes in, and you have two main roads you can take: Personal (using a Pre-Shared Key, or PSK) and Enterprise (using a protocol called 802.1X).
Picking the right path here is one of the most important security decisions you'll make for your organization.
Think of PSK as the single key to your house. Everyone who needs to get in—family, friends, the pet sitter—gets a copy of the exact same key. It's simple, and it works just fine for a home network.
But in a business, Retail, or Education setting? That single key becomes a security nightmare waiting to happen. What happens when an employee leaves or a student graduates? You're stuck changing the password for everyone and reconfiguring every single device. It's a massive operational headache and a huge security gap.
Worse, you have no real way of knowing who is doing what because everyone is using the same shared identity. This is especially dangerous in BYOD Corporate environments where individual accountability is non-negotiable.
The Clear Winner for Business: Enterprise Authentication
This is precisely where Enterprise authentication, also known as WPA2/WPA3-Enterprise, changes the game.
Instead of one shared key for the whole building, this method gives every single user their own unique "ID badge" with their personal login credentials (typically the username and password they already use for their computer or email). For any serious network, this is the gold standard.
WPA3-Enterprise authentication with 802.1X isn't just about securing the network—it's about creating individual accountability. You get a clear, auditable trail of who is connecting, from what device, and when. It’s a level of control and insight that PSK simply can't provide.
So, how does it work? When a user tries to connect, their device presents its credentials to a Cisco or Meraki access point. The access point doesn't make the decision itself; instead, it checks with a central authentication server (known as a RADIUS server) to verify the user's identity before granting access.
This approach delivers some powerful advantages:
- Individual Access Control: When someone leaves, you just disable their account. No one else is affected.
- Airtight Security: Each user's connection is individually encrypted, meaning no one else on the Wi-Fi can snoop on their traffic.
- Seamless User Experience: It can integrate directly with existing user directories like Azure AD, so people log in with the same credentials they use for everything else. One less password to remember.
To really dig into the specifics, check out this detailed comparison of WPA2-Enterprise vs Personal authentication and see why Enterprise mode is the only logical choice for organizational security.
Advanced Security with IPSK and Captive Portals
When you move past using a single password for everyone, you unlock some seriously powerful and flexible ways to manage your Wi-Fi. This is where modern authentication really starts to shine, especially for the guest access and Bring Your Own Device (BYOD) situations you see every day in Retail, Education, and Corporate settings. Let's dig into two game-changing approaches.

First up is Identity Pre-Shared Key (IPSK), sometimes called EasyPSK. I like to think of it as the perfect middle ground—it's way more secure than a simple shared password but avoids the heavy lifting of a full Enterprise setup. Instead of one password for the masses, IPSK gives a unique, personal password to each user or device.
This is a massive security upgrade. Think about it: if an employee leaves or a student's tablet gets lost, you just revoke that one specific key. Nobody else is affected. This makes it an ideal type of security for wifi in schools trying to manage hundreds of student devices or in offices that need a secure way to get contractors and their gear online safely.
The Power of Captive Portals for Guest WiFi
Next, let's talk about Captive Portals. You’ve definitely run into these. They’re the branded login pages that pop up when you connect to the Wi-Fi at a hotel, airport, or your local coffee shop. They're much more than just a login screen; they're a powerful tool for secure onboarding and user engagement.
A captive portal basically acts as a doorman for your network. Before anyone gets full internet access, they have to interact with this page first. That interaction can be almost anything you want it to be, which lets you create a completely customized and controlled experience.
Captive Portals transform a simple connection into an opportunity. They provide a secure entry point that can be used for branding, communicating terms of service, or gathering user consent, all while keeping your internal network completely separate and safe.
This controlled access is a must-have for any business offering guest wifi. It makes sure that every single user is identified and agrees to your usage policies before they get online. High-performance hardware from brands like Cisco and Meraki is perfectly suited for this, giving you the reliable backbone needed for a consistently smooth user experience.
Creating a Seamless User Experience with Social Login
One of the best features of a modern captive portal is the social wifi login. This lets guests use credentials they already have—like Google or Facebook—to get online. For the user, it’s a quick, one-click way to connect without having to remember yet another password. For the business, it can provide valuable, opt-in demographic data to help you understand your customers better.
This method completely streamlines the login process and gets rid of the friction of creating a new account. The result? A better experience for your guests and smarter data for your business.
For those who want to dive deeper into advanced setups, you can learn more about how to combine IPSK with RADIUS authentication for even more granular control. By pairing strong encryption with user-friendly authentication solutions like these, you can build a network that’s both incredibly secure and incredibly easy to use.
Putting Wi-Fi Security to Work in Your Industry
Theory is one thing, but seeing how different security methods perform in the real world is what really matters. Different industries have completely different needs, so a cookie-cutter approach to network security is bound to fail. Let's look at how to apply these concepts where it counts: in Education, Retail, and Corporate settings.
This isn't just about choosing a technology off a list. It’s about creating a security blueprint that fits how you actually operate, often built on a solid foundation of hardware from providers like Cisco and Meraki.
Security for the Education Sector
Schools and universities are some of the most challenging wireless environments out there. They are the classic BYOD (Bring Your Own Device) free-for-all, with thousands of student and staff devices all needing a secure and stable connection. Handing out a single shared password would be a nightmare to manage and a huge security hole.
This is where IPSK (sometimes called EasyPSK) is a perfect fit. It gives IT admins the power to issue a unique pre-shared key to every single person.
- Painless Onboarding: New students can get their own key automatically, making it simple to get connected.
- Clear Accountability: If a student loses their laptop or leaves the school, you can kill their key in seconds without disrupting anyone else.
- Controlled Access: You can assign different keys for different access levels, keeping student devices away from sensitive staff resources.
For the Education sector, IPSK hits the sweet spot. It delivers the granular device security of a much more complex system but keeps things simple enough to manage a huge, ever-changing user base.
Boosting Engagement in Retail
In Retail, the game changes completely. The priority isn't just internal devices; it's the public. Great guest Wi-Fi is now a basic expectation that can make or break the customer experience. But you have to offer it without opening a backdoor to your critical systems, like Point-of-Sale (POS) terminals.
This is a job for Captive Portals. By funneling guests through a branded login page, retailers create a secure gateway for shoppers. The portal walls off all guest traffic from the private company network, completely neutralizing the risk.
But a captive portal is more than just a security guard. It’s a fantastic marketing tool. By adding social login options, you create a frictionless social Wi-Fi experience. Shoppers connect with one click using their existing accounts, giving your business valuable (and permission-based) demographic data in return. To see how these tools fit into a bigger picture, check out our overview of different WiFi solutions for business.
The Hybrid Approach for Corporate Environments
The modern BYOD Corporate world demands a mix of strategies. You need ironclad security for employee connections but also a simple, secure, and professional way to get visitors online. That calls for a two-track approach.
For any company-owned devices and employee personal devices, WPA3-Enterprise should be the gold standard. It delivers the robust encryption and individual user authentication needed to protect sensitive corporate data. No compromises here.
For guests, a polished Captive Portal is the way to go. It offers a professional, branded welcome mat for visitors, contractors, and clients. This keeps their traffic safely separate from your internal network while upholding your company's professional image. It's a hybrid model that secures internal assets without giving visitors a headache.
How to Implement Modern WiFi Security
Knowing the theory behind Wi-Fi security is great, but putting it into practice is a whole different ball game. The first, most critical step is upgrading your network to a modern protocol like WPA3. This move alone provides a massive boost, protecting against brute-force password attacks and making connections safer, especially on public or open networks.
But let's be realistic—the path to a fully upgraded network is rarely a straight line.
One of the biggest headaches you'll run into is backward compatibility. Your shiny new Cisco and Meraki access points are all set for WPA3, but what about everything else? You've got older printers, laptops, and countless other devices that can only handle WPA2. This is a daily reality in BYOD Corporate offices and across sprawling Education campuses.
Bridging the Gap with Transition Mode
Thankfully, network hardware manufacturers saw this problem coming. Most enterprise-grade access points now offer a "transition mode" for WPA2/WPA3, which is an absolute lifesaver. This clever feature lets your network broadcast both security protocols at the same time.
What does that mean for you? Your newer, WPA3-capable devices get to connect with the best security available, while your older legacy gear can still hop on the network using WPA2. It creates a smooth migration path, allowing you to beef up your security without having to abandon older, but still perfectly functional, hardware. We dive deeper into how protocols like 802.1X fit into these modern authentication solutions in our other guides.
WPA3, which came out in 2018, was built from the ground up to fix the flaws in older protocols. It uses a technology called Simultaneous Authentication of Equals (SAE) that makes it incredibly difficult for attackers to crack your Wi-Fi password. With new standards like Wi-Fi 6E and Wi-Fi 7 actually requiring WPA3, its adoption is on the rise. Still, managing backward compatibility is the main puzzle most organizations are trying to solve.
Thinking about security holistically is key, especially as more devices come online. For example, to secure your entire smart home, you might want to check out the ultimate guide to Smoke Detector WiFi for comprehensive home safety. Choosing the right type of security for wifi isn't just for your computers and phones—it's for every single thing that connects.
Navigating Your WiFi Security Questions
Let's clear up some of the most common questions people ask when setting up their network security. Getting a handle on these concepts will help you build a network that’s not just secure, but also easy for everyone to use.
What’s the absolute best WiFi security I can get?
If you're looking for the top of the mountain, it's WPA3-Enterprise. No question.
It's a powerful combination: you get the rock-solid encryption of WPA3 paired with the robust authentication of 802.1X. Instead of a single shared password, every single person gets their own unique login credentials. This gives you iron-clad control and a clear audit trail, which is why it's the gold standard for corporate offices, universities, and any place where data security is non-negotiable.
Can I still use a Captive Portal if my network has WPA3 encryption?
You bet. Think of them as two different layers of security that work together beautifully.
First, you lock down the airwaves with strong WPA2 or WPA3 encryption—that’s your foundational security. The Captive Portal then sits on top of that, managing who gets on the network and how they do it (like with a social login or a simple form). The user's connection stays fully encrypted the entire time.
What is IPSK, and where does it fit in?
IPSK, or Identity Pre-Shared Key, is the perfect middle ground between a single, shared password for everyone and a full-blown Enterprise setup. We sometimes call it EasyPSK because it makes life so much simpler.
With IPSK, you can generate a unique password for every user or even every single device. It's a fantastic solution for Bring Your Own Device (BYOD) environments in schools or offices running on hardware from vendors like Cisco or Meraki. You get the accountability of knowing who is who, and if someone leaves, you can just revoke their key without affecting anyone else.
As you explore these options, it's also wise to consider what data is being collected and why. For a good primer on this, check out this guide on understanding privacy and data collection.
Ready to put these advanced security solutions to work? Splash Access offers powerful captive portal and IPSK integrations built for Cisco Meraki that you can deploy in minutes. Explore our features today.




